[Abstract] BB84 (quantum key distribution protocol) is excellent among the limited applications when using a single qubit (that is, not using quantum entanglement). I've written an article about this in the past, but I'll add it here to make it even clearer. This BB84 is also a good example for learning "measurement of quantum states by orthonormal basis".
●What is BB84 (reconfirmation)
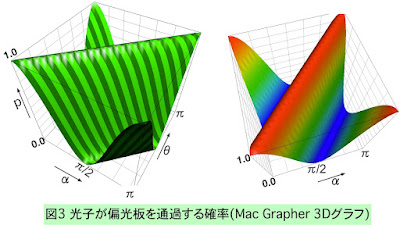
BB84 is a method in which 1/4 of Alice's classical bit string of length 4n is used as a secure key between them without sending it directly to Bob. Alice randomly selects an orthonormal basis for each bit of the classical bit string of length 4n, and sends the basis vector (quantum state vector) corresponding to that bit to Bob. Importantly, a method is included to determine if this transmission has been intercepted by a third party, Eve.
●Blog articles written in the past
I wrote the BB84 method in detail in the blog post below. (The figure is also reproduced.)
https://sparse-dense.blogspot.com/2022/11/bb84.html
----------(Supplementary explanation added)----------------------------
●How to actually configure the BB84
The theory is now explained. From the above explanation, the number of times Alice and Bob's chosen bases match is 2n. The resulting bit string measured by Bob on that matched base matches the bitstring Alice has. So, assuming no eavesdropping, Alice does not send the 2n long bit string to Bob and they can both share the bit string as a key.
However, in reality, Alice is sending the basis quantum state vector to Bob, so we have to check whether it is wiretapped. Therefore, both parties send each other n-length bit strings, which is half of this 2n-length bit string, by "unencrypted normal communication" and confirm the degree of matching. If they match perfectly, it can be said that there is no eavesdropping. On the other hand, if 1/4 of them do not match, it can be said that there was wiretapping. (It takes advantage of the fact that eavesdropping requires measuring its qubit (quantum state vector), which changes the quantum state to be sent to Bob.)
If we find no eavesdropping, we can safely use the other half of the matched 2n long bit string as the key. (Actually, 2n lengths match, but half of them may be known to others due to the above-mentioned normal communication.)